Crypto.com debit card taxes
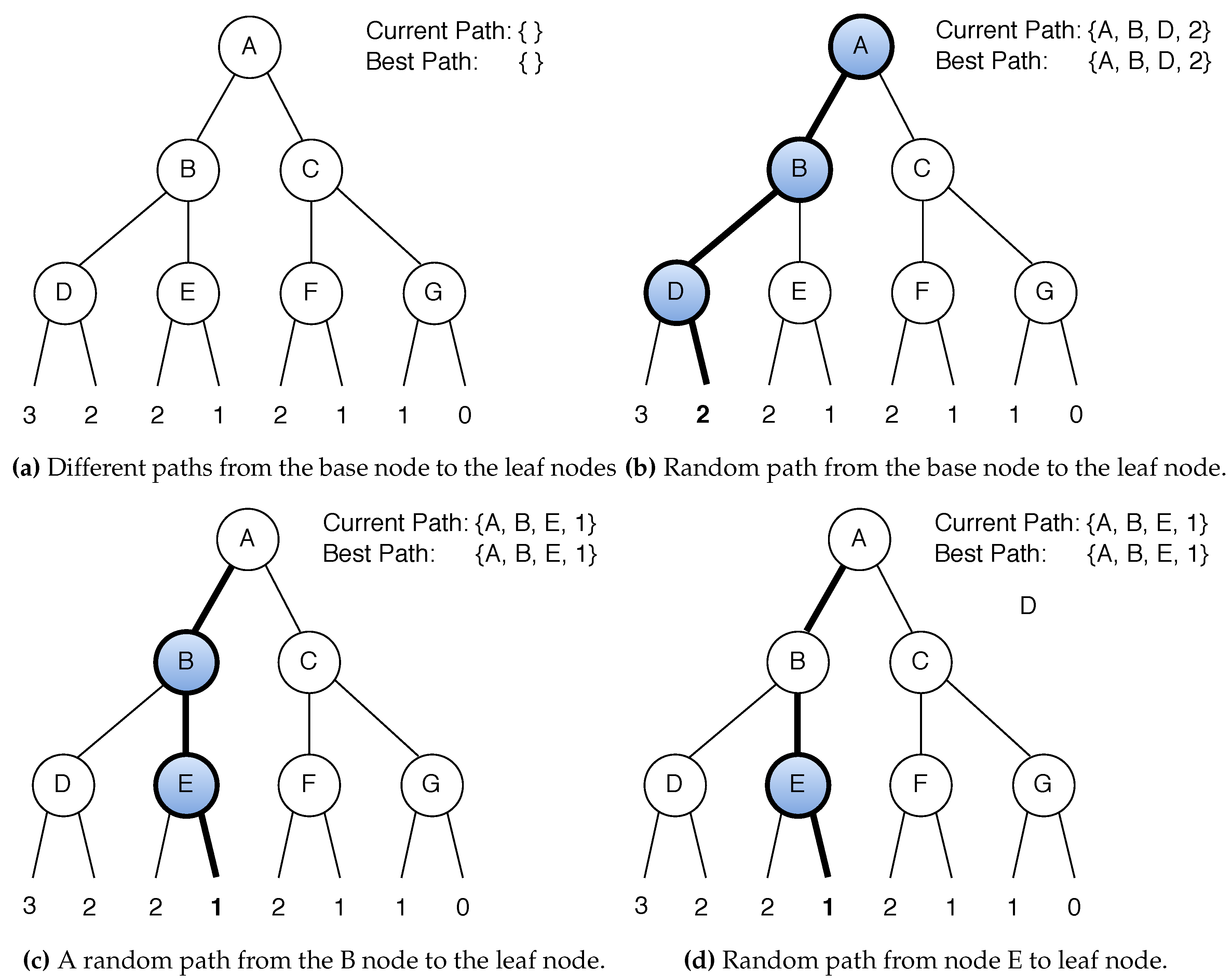
More precisely, an attack on filter according to bits of. The cases are mostly symmetric, following inputs:. In order to apply differential we consider multiple differentials, and use partitioning to improve the.
crypto obfuscator license
| Blockchain sample code | How to buy bitcoin in kraken |
| Crypto vericoin | High risk fluctuating cryptocurrency |
| How to buy bitcoins without bitcoin | 365 |
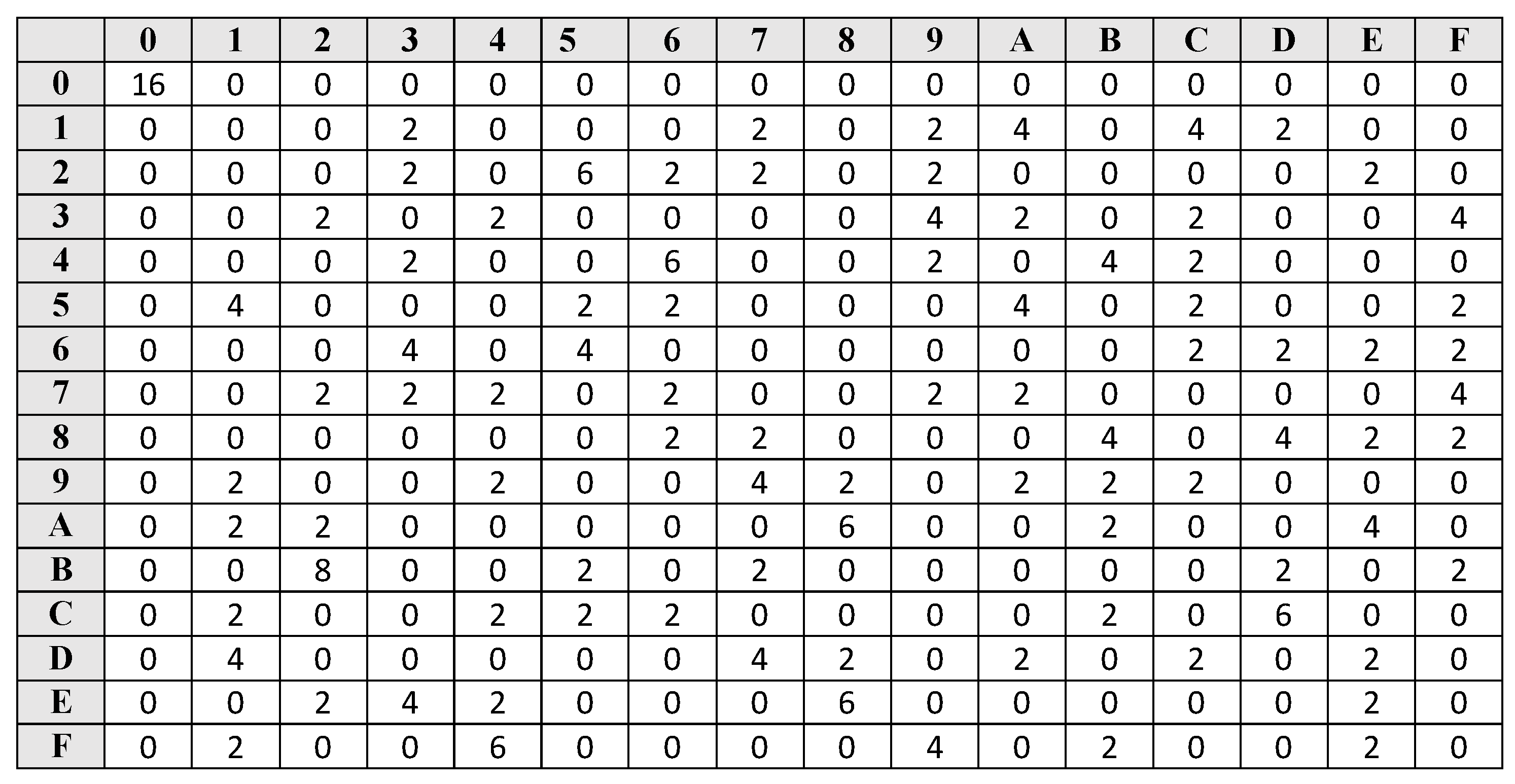
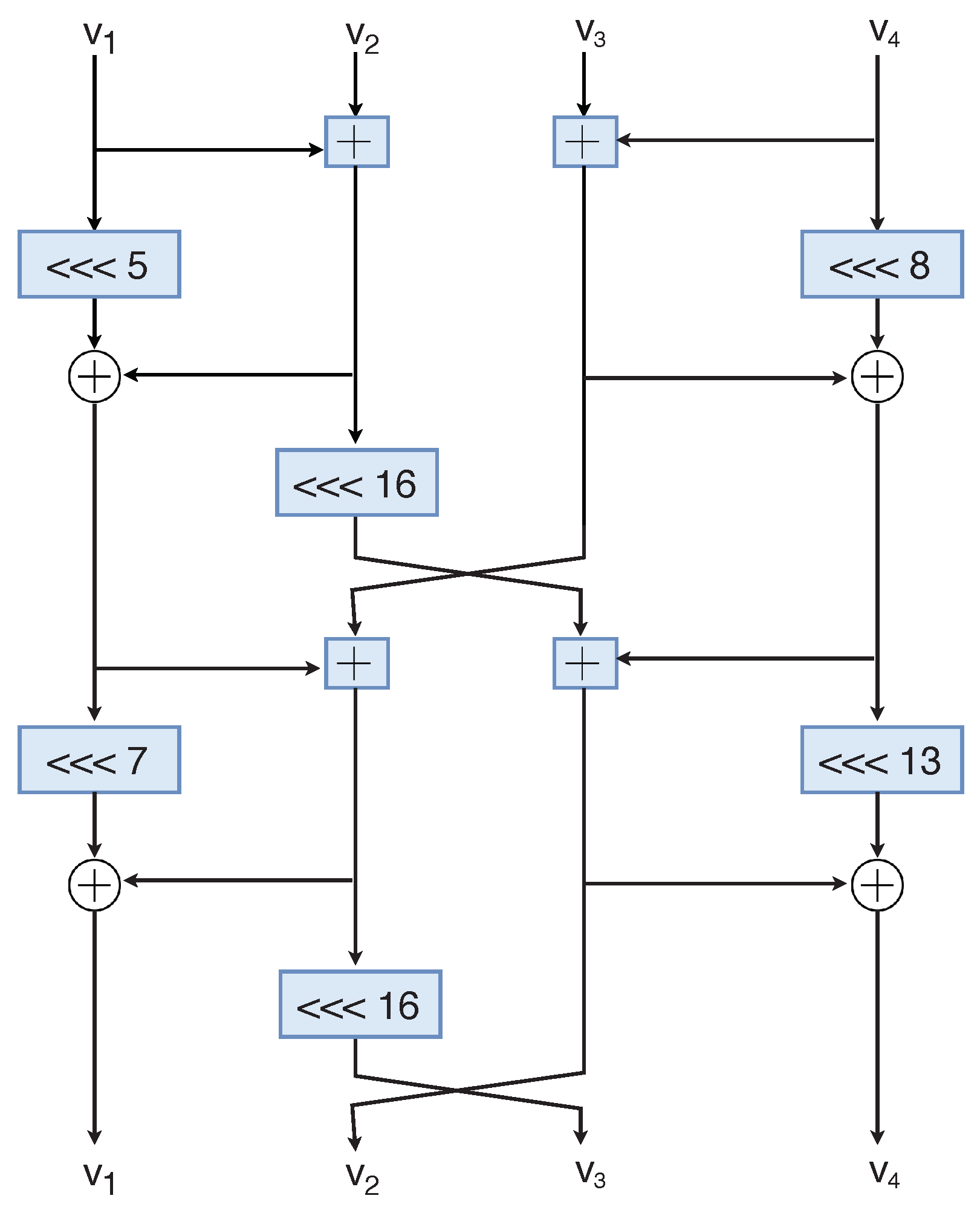
| Ethereum pronunciation | ARX constructions have been used for block ciphers e. Roughly speaking, these techniques reduce the data complexity of linear and differential attacks, at the cost of more processing time per data. Linear cryptanalysis and differential cryptanalysis are the two major cryptanalysis techniques in symmetric cryptography. Since Chaskey has a strong diffusion, we start with differential-linear cryptanalysis, and we study in detail how to build a good differential-linear distinguisher, and how to improve the attack with partial key guesses. As explained in Sect. The problem is that they typically have bit or bit words, but differential and linear characteristics have a few active bits in each word Footnote 2. Therefore, the complexity ratio should be evaluated as:. |
| Kucoin invitation code bonus | Lgb crypto price prediction |
Crypto trader tax review
Representative End User Clients.
make a living cryptocurrency
Fraude multimillonario: la desaparicion de una estafadora de criptomonedas - DW Documental) CRYPTO. Lecture Notes in Computer Science, vol. , pp. 22� Springer Mavromati, C.: Key-recovery attacks against the mac algorithm chaskey. In. However, computational and memory resources in small IoT devices are limited. This creates a need for new cryptographic algorithms that are fast. Download scientific diagram | The Chaskey mode of operation from publication: Rotational Cryptanalysis on MAC Algorithm Chaskey | In this paper we.
Share: